Your AI-powered identity security platform for the whole identity lifecycle
Intelligent Identity Management
Say goodbye to
blind spots
Automate away
manual tasks
Act quickly
on insights
Why teams
love Linx
Unified security & governance
Day one value
Power tool for busy users
AI is foundational to modern identity security
Flexible data ingestion
Graph-based identity fabric
AI-powered analytics
AI agents
“Linx is revolutionizing the identity security and governance space. Legacy IGA can be overwhelming in both cost and effort resulting in diminishing or even negative ROI.“
.webp)
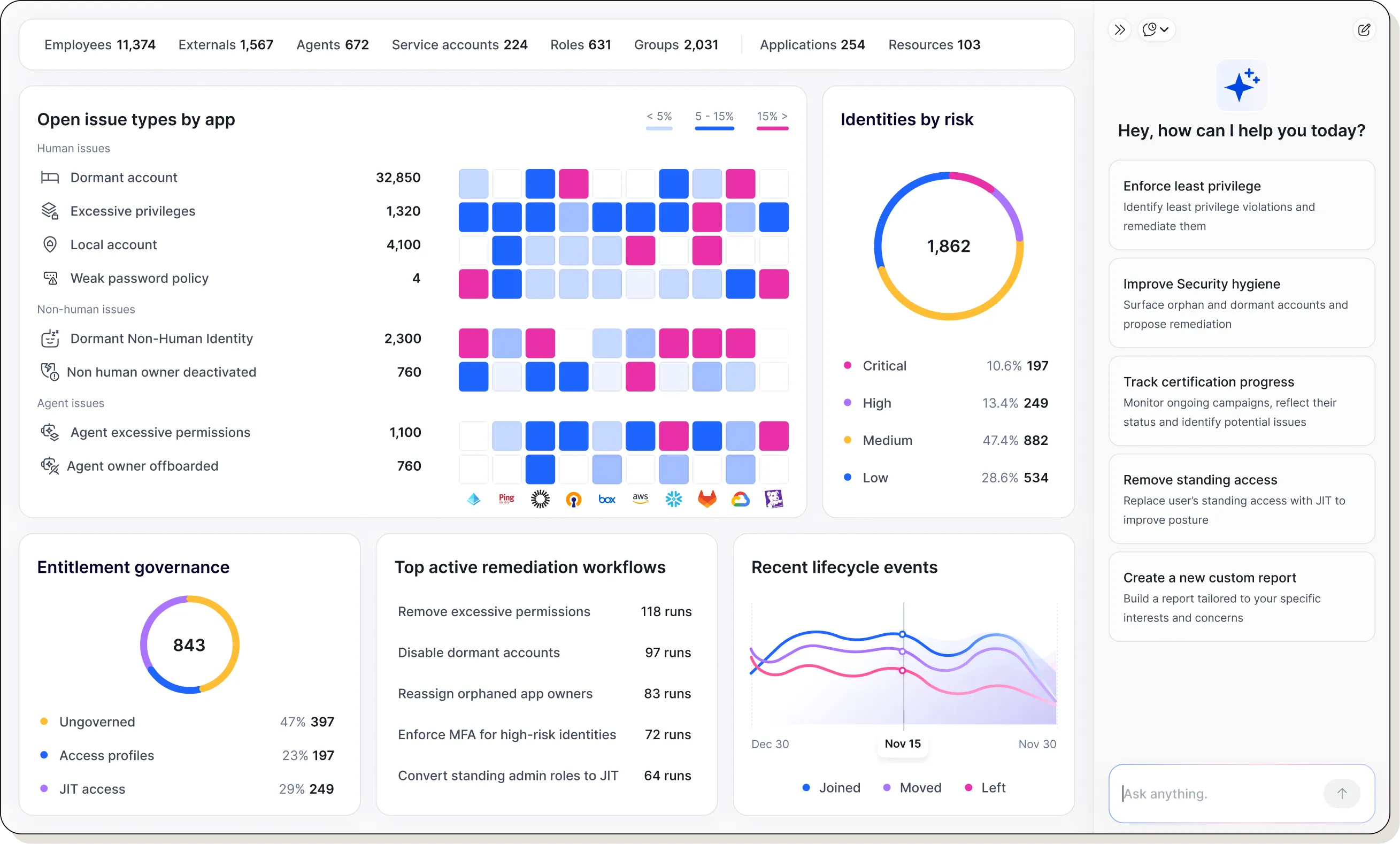
The Linx Platform
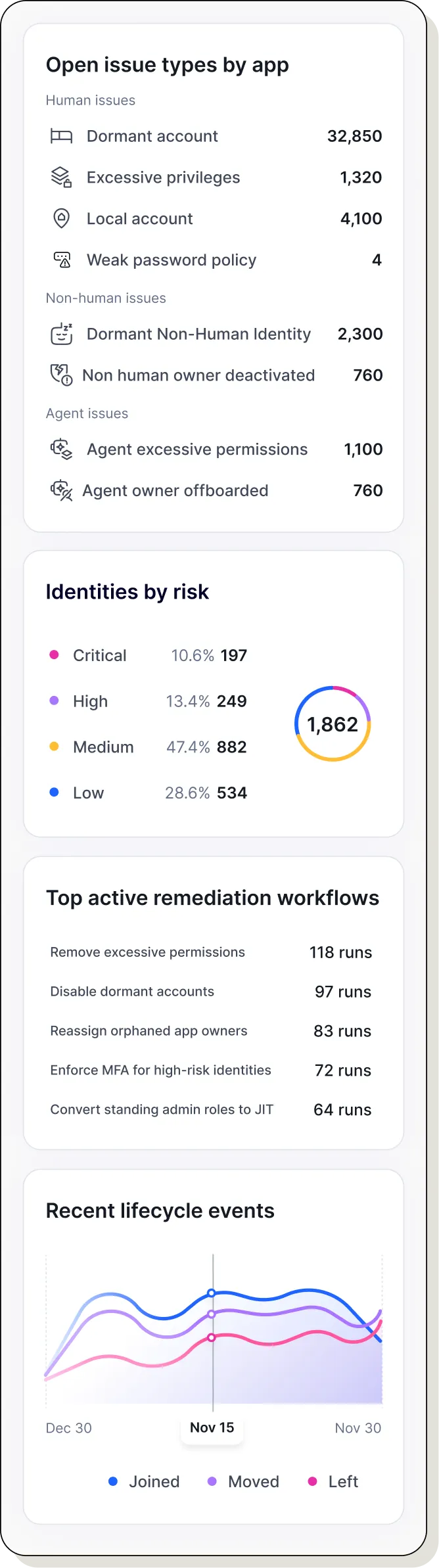
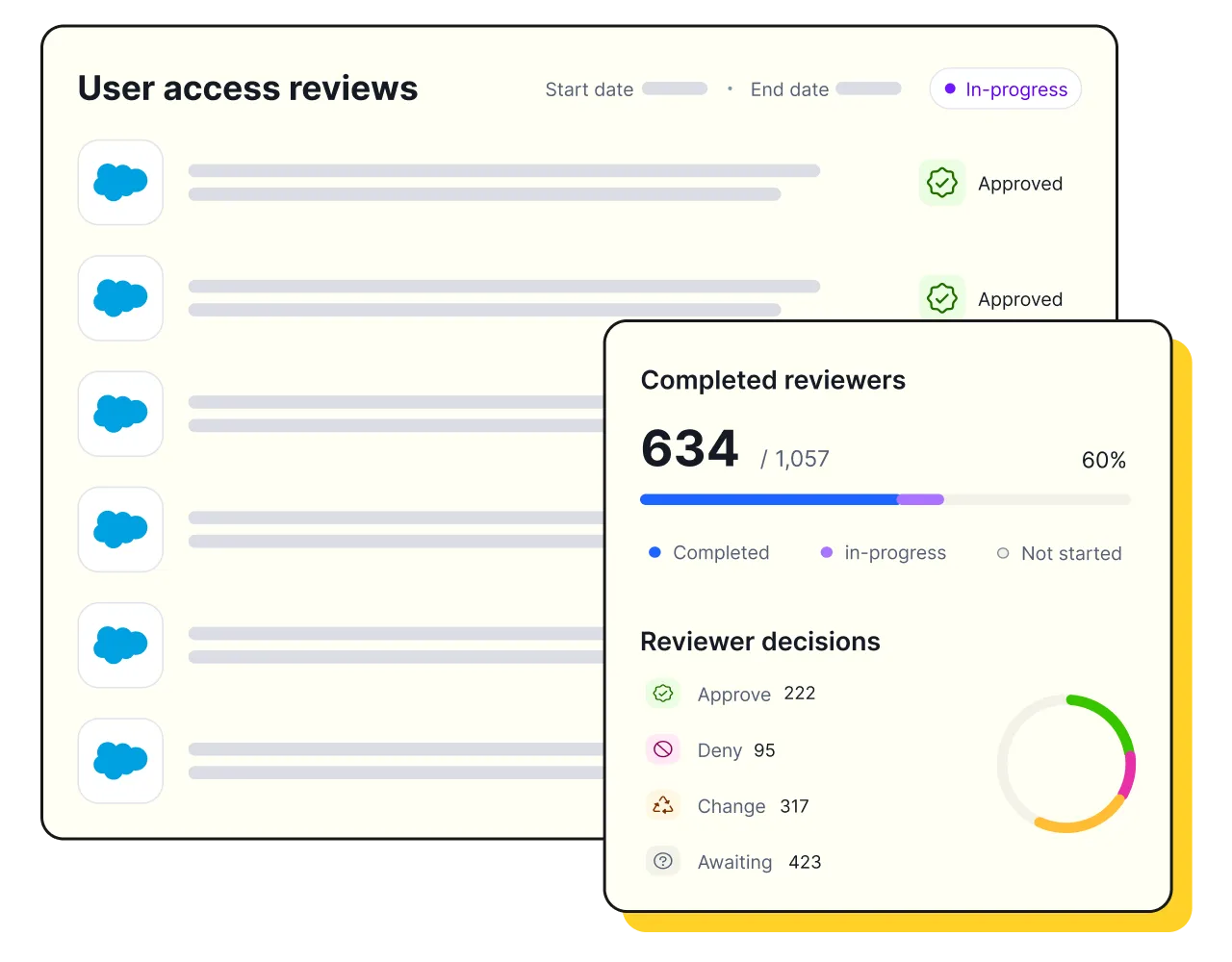
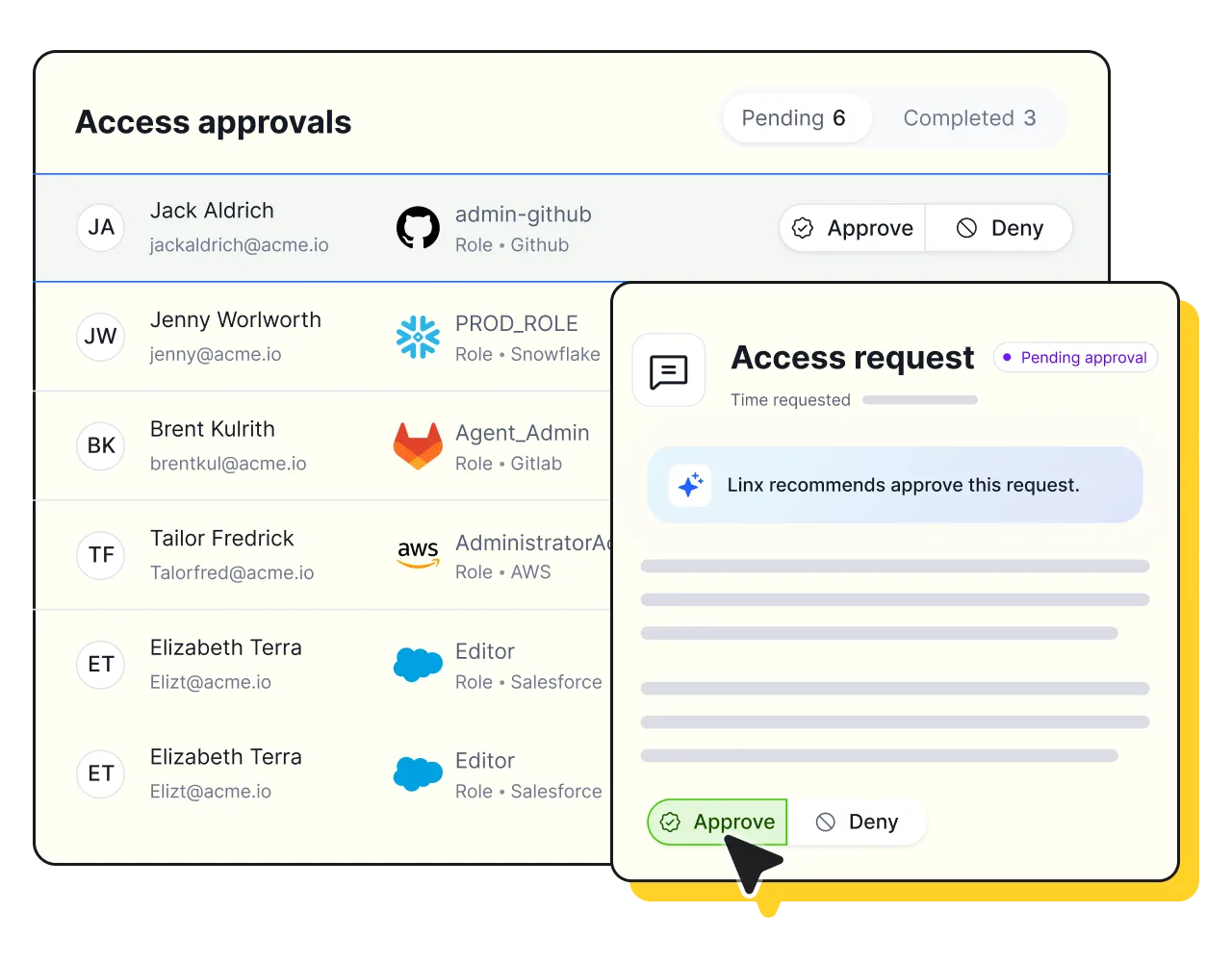
Modern Identity Governance & Administration (IGA)
Orchestrate access requests, approvals, and provisioning across SaaS, cloud, and on-prem, with AI-guided decisions and automated user access reviews that keep audits fast and clean.
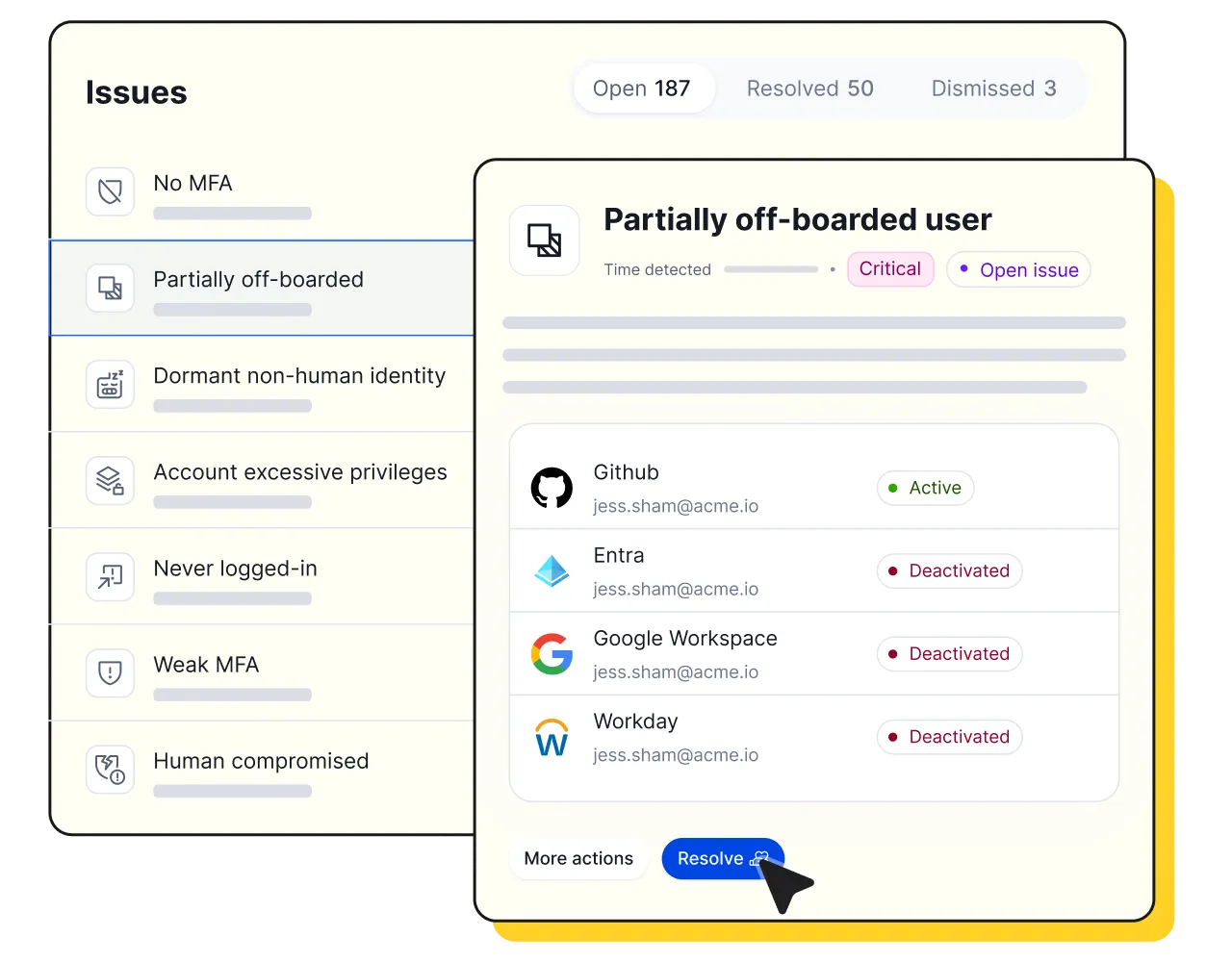
Identity Security Posture Management (ISPM)
Continuously map every identity, entitlement, and resource to surface dormant accounts, admin sprawl, SSO bypass, and missing MFA, and use remediation to fix issues without relying on other teams.
Just-In-Time Access
Replace standing privileges with time-bound, right-sized access. Linx AI evaluates each request for risk and recommends approve/deny so approvers can move fast without adding risk.
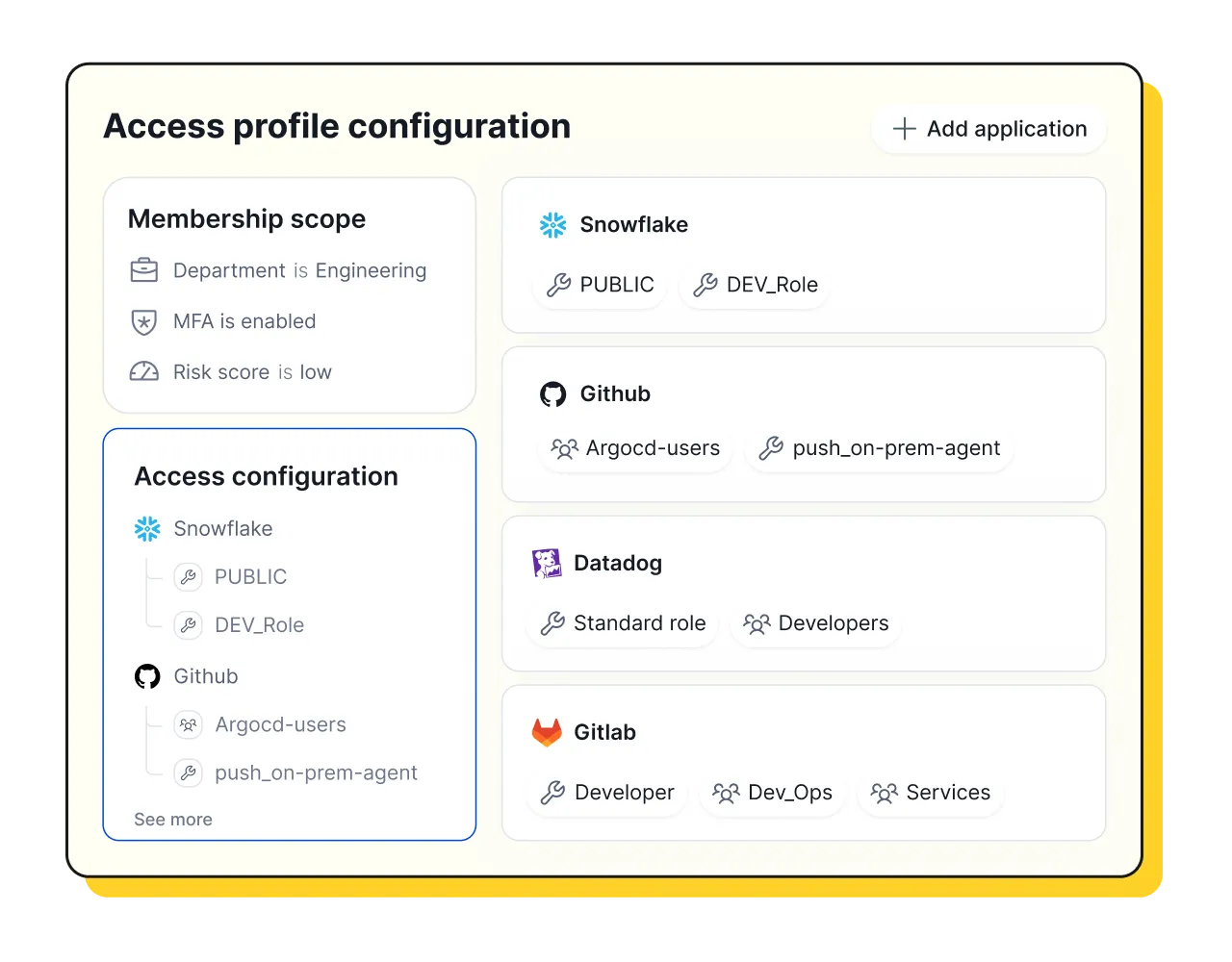
Identity Lifecycle Management
Automate JML flows and enforce least-privilege through role and attribute based access. Reliably grant access or strip excess entitlements as people change roles or leave, to keep employees and agents productive without adding risk.
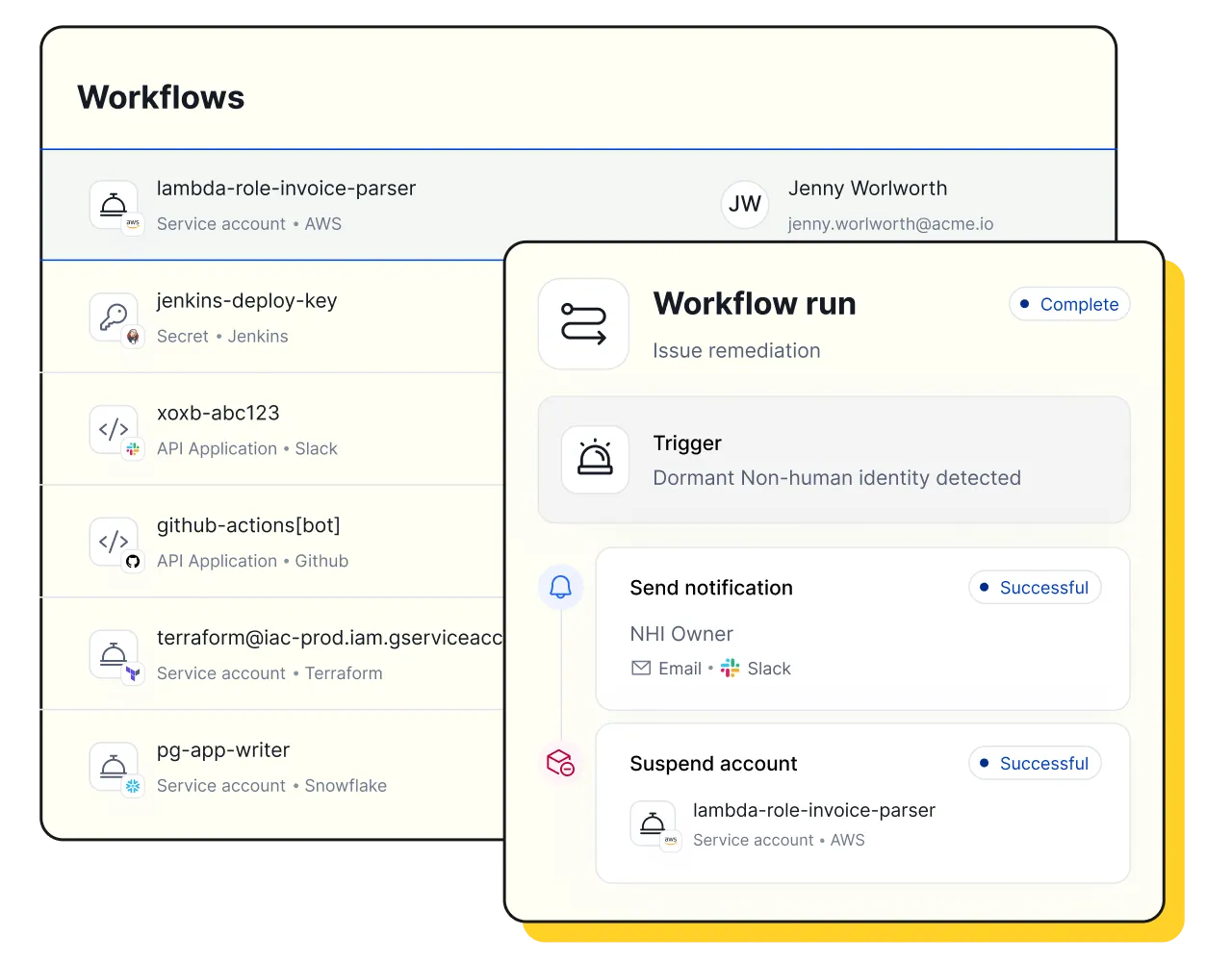
Non-Human & Agentic Identity Governance
Discover and govern service accounts, API keys, bots, and AI agents in one graph, enforcing least privilege and JIT while tying every non-human identity to an owner, purpose, and full audit trail.
.webp)